As a software engineer who creates industrial security technologies I am often asked “Why are industrial networks so hard to secure?” This is a big topic, so today I will address only “Why are PLCs so insecure?”
 News
News
 Compact Industrial Gateway for High-Speed Data Transfer
Compact Industrial Gateway for High-Speed Data Transfer
 Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
 Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises
Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises
As a software engineer who creates industrial security technologies I am often asked “Why are industrial networks so hard to secure?” This is a big topic, so today I will address only “Why are PLCs so insecure?”

With the acquisition of Tripwire in 2015, Belden expanded its industrial cyber security offerings to include proactive security monitoring and regulatory compliance solutions. While Tripwire is a leading security and compliance vendor in a number of different industries, such as retail, government and financial services, what do their solutions bring to ICS security?

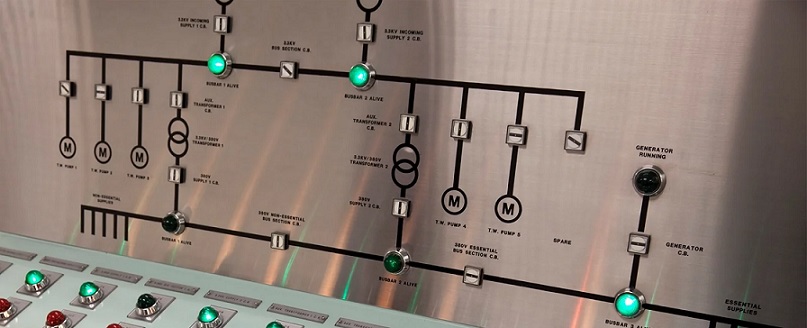
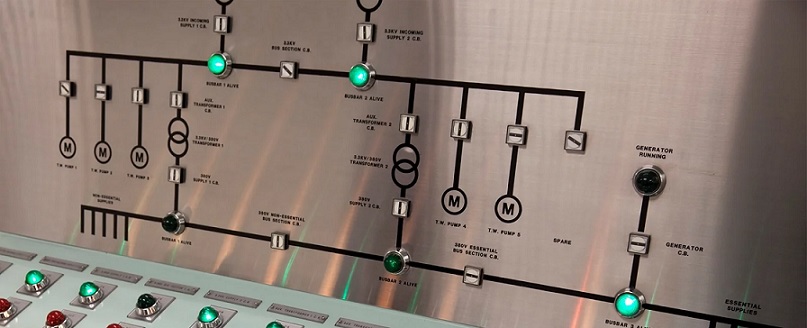
This week, the largest electric utility trade show and conference in the U.S., DistribuTECH, is being held. One of the tracks in the conference portion of the event is “Defending the Grid.” The prominence of the topic at this show is due in part to new NERC CIP requirements designed to strengthen reliability and security. Another reason grid protection is a hot topic is high-profile cyberattacks such as the recent one on the Ukraine power system.

While there have been numerous high profile cyberattacks on industry over the past few years, their consequences have primarily been to steal information (Dragonfly, Flame, Duqu) or interrupt business operations (Shamoon). Stuxnet and the attack on the German steel mill were rare cases where a control system was disrupted as a result of a malware infection.

The start of a new year is often the time we make decisions to do things differently than in the past. Today I would like to suggest that one of the 2016 decisions you make is to toss out invalid ICS security assumptions and hone in on meaningful improvement for your cyber security defenses.
 Languages
Languages
 Blog categories
Blog categories
 Newsletter
Newsletter