
If you have read my previous blogs on patching for control system security, you might think I am completely against patching. Guess what? I’m not against them!
 News
News
 Compact Industrial Gateway for High-Speed Data Transfer
Compact Industrial Gateway for High-Speed Data Transfer
 Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
 Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises
Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises

If you have read my previous blogs on patching for control system security, you might think I am completely against patching. Guess what? I’m not against them!
In my last blog, I discussed the reasons why critical industrial infrastructure control systems are so vulnerable to attacks from security researchers and hackers, and explained why patching for such systems is not a workable solution.

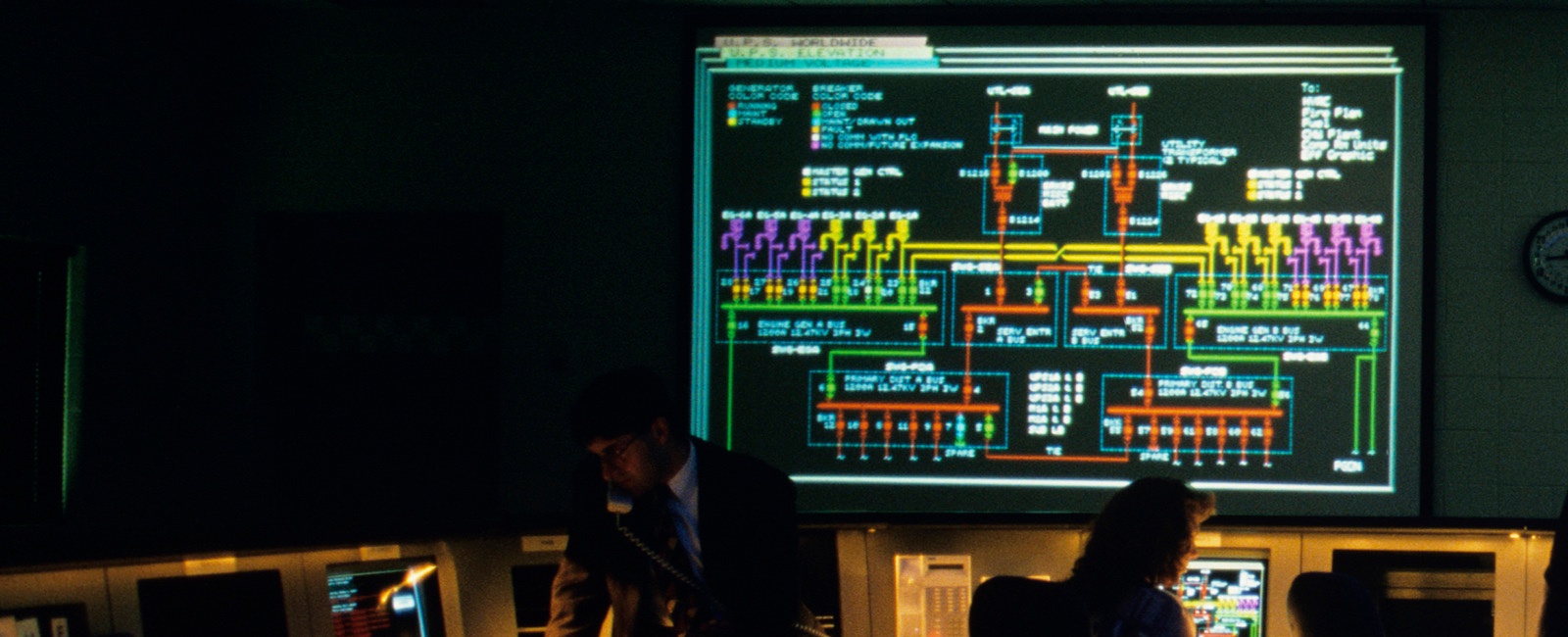
As regular readers of this blog know, after Stuxnet, security researchers and hackers on the prowl for new targets to exploit shifted their efforts to critical industrial infrastructure. Unfortunately, the Supervisory Control and Data Acquisition (SCADA) and Industrial Control Systems (ICS) applications they are now focusing on are sitting ducks.

Last week I received am email (shown further down on this page) purporting to be from the US Internal Revenue Service (IRS).

It wasn’t that long ago when cyber security seemed like a foreign language to those folks entrusted with running companies. It was not like they didn’t know about it, but it just was not top of mind. Not anymore.
 Languages
Languages
 Blog categories
Blog categories
 Newsletter
Newsletter