
Who is responsible for fixing the thousands (some say 100,000) of vulnerabilities that exist in PLCs, DCS, RTUs and other automation devices that are in use in facilities around the world?
 News
News
 Compact Industrial Gateway for High-Speed Data Transfer
Compact Industrial Gateway for High-Speed Data Transfer
 Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
Getting Started: Cross-Site Remote Management for ADAM Modbus I/O with EdgeHub
 Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises
Advantech and Qualcomm Strengthen Collaboration to Accelerate Innovations with AI On Premises

Who is responsible for fixing the thousands (some say 100,000) of vulnerabilities that exist in PLCs, DCS, RTUs and other automation devices that are in use in facilities around the world?

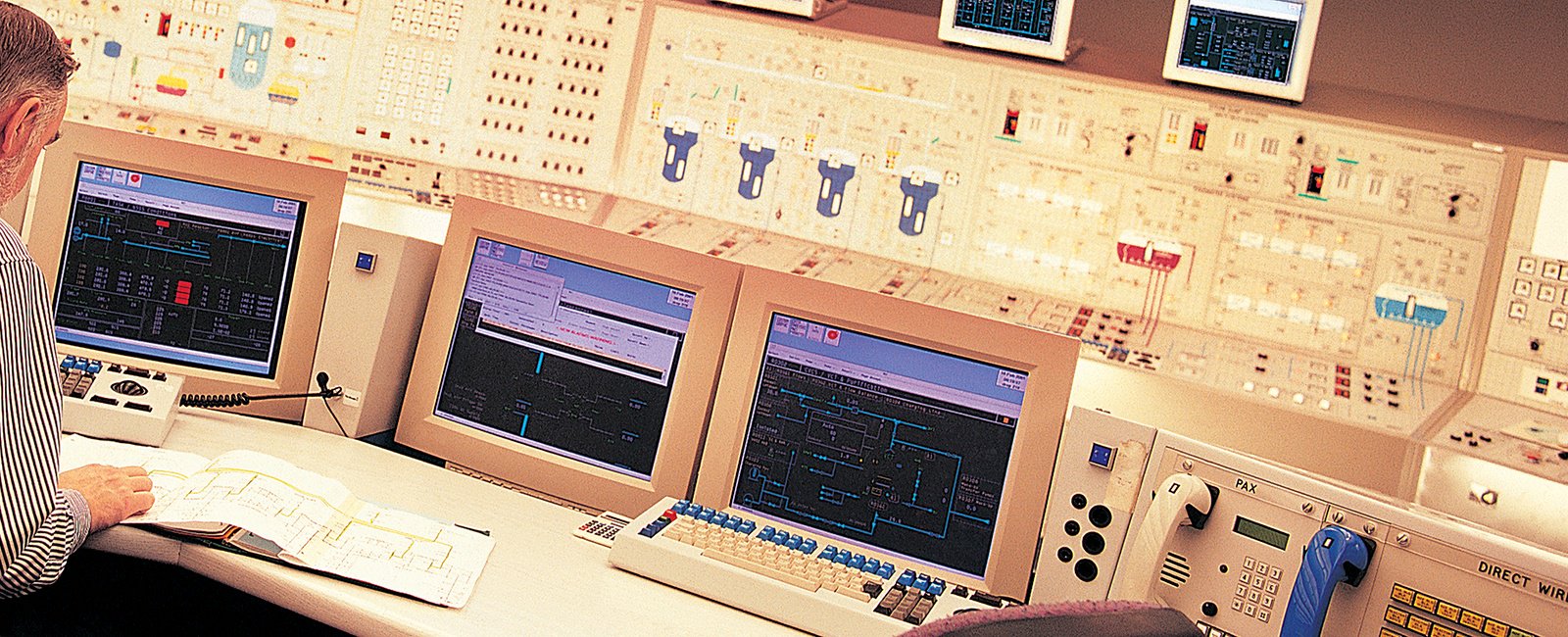
In last week's blog, Heather wrote an excellent summary of Mark Cooksley's network security presentation regarding "Why Industrial Networks are Different than IT Networks". In it she noted that the number one goal of ICS security is based on the concern for safety. This is spot-on in my opinion. However, there is more to consider when it comes to industrial security priorities…

Previously we looked at the question of 'Why are PLCs so insecure?' Today we are going to come at SCADA security from another angle, which is 'Why is securing Industrial Networks different than securing IT Networks?' We will also look at three ways to address these differences.

Last week I wrote about a serious issue in the patching of SCADA and ICS systems. Just when you think you are installing all needed patches, some critical ones are getting missed.
Yesterday afternoon I received a note from another security expert that has left me a bit stunned. Like most of you, I assumed that if you are patching your Windows computers on your SCADA or ICS system (using some variation of Microsoft Windows Update), then any vulnerable services that can be patched will be patched. Well guess again – you may still have a number of open vulnerabilities that are happily being missed by the Windows update service. And scariest of all, you can’t do much about it.
 Languages
Languages
 Blog categories
Blog categories
 Newsletter
Newsletter